WIN33 is considered a formidable toolkit designed specifically for abusing vulnerabilities within the Windows. This platform empowers ethical hackers to locate and exploit these vulnerabilities, ultimately aiding in the improvement of system security.
- WIN33's offer a extensive range of tools and modules for activities including
Unveiling the Secrets of WIN33
WIN33, a mysterious relic of the ancient era, has captured the imaginations of tech enthusiasts for decades. This complex program, with its unclear origins, holds hidden knowledge that could unlock the early days of computer science.
Dedicated researchers are persistently analyzing WIN33's structure, hoping to {uncover its purpose. Each piece of data unearthed brings us steadily to deciphering this complex artifact.
Harnessing with WIN33
WIN33 is a powerful arsenal for elite weaponization. It provides unparalleled capabilities to exploit systems. By utilizing WIN33's adaptability, you can execute a wide range of tasks. From neutralizing infrastructure, to exfiltrating sensitive data, WIN33 empowers you to control the digital landscape. Understanding its intricacies is essential for aspiring threat actor looking to achieve success.
- Study the core principles of WIN33.
- Experiment its modules in a controlled environment.
- Keep updated on the latest techniques.
Offensive Hacking with WIN33: A Comprehensive Guide
Diving into the world of ethical hacking can be both intriguing, but it's crucial to approach it with a solid foundation. WIN33, a versatile platform, empowers aspiring hackers to hone their skills in a secure environment. This thorough guide will guide you through the fundamentals of ethical hacking using WIN33, covering key concepts and practical techniques. From vulnerability assessment to penetration testing, we'll empower you with the knowledge and tools to master the complex landscape of cybersecurity.
Ethical hacking isn't just about exploiting vulnerabilities; it's about uncovering them to fortify security. WIN33's intuitive interface and robust website features make it an ideal tool for both beginners and experienced professionals.
- Understand the basics of network security and common vulnerabilities.
- Utilize WIN33's tools to perform vulnerability scans and penetration tests.
- Build your ethical hacking skills through hands-on exercises.
- Keep up-to-date with the latest security threats and trends.
Vulnerability Assessment WIN33: Advanced Techniques
Utilizing the power of WIN33 allows penetration testers to perform advanced techniques that go beyond conventional methods. This platform provides robust tools and functionalities for analyzing networks, identifying vulnerabilities, and reproducing real-world attacks. WIN33's advanced features comprise custom payload creation, automated attack execution, and detailed reporting functions.
Moreover, WIN33's scalable architecture allows testers to tailor their toolset based on specific objectives. Through leveraging WIN33's advanced techniques, penetration testers can conduct more effective assessments, uncovering critical vulnerabilities that may otherwise go unnoticed.
The Evolution of Attack Frameworks: WIN33 and Beyond
From its emergence in recent years, the field of cyber security has witnessed a relentless evolution in attack frameworks. Early frameworks like WIN33, with its dedication to lateral movement and stealthy operations, laid the blueprint for future generations of attackers. However, the threat landscape is constantly evolving, demanding a relentless adaptation in attack strategies. Contemporary adversaries are leveraging cutting-edge tools and techniques that push the boundaries of traditional security protocols.
This evolution is observable in the emergence of new frameworks, each with its own peculiar set of capabilities and objectives. Frameworks like Empire, for instance, offer a enhanced of flexibility to attackers, allowing them to conduct complex missions with increased payload. In addition, the rise of machine learning attacks is ushering in a new era where adversaries can adapt their tactics in real-time, making it even more challenging for defenders to keep pace.
As the cyber threat landscape persists to evolve at an accelerated rate, grasping these emerging attack frameworks is vital for organizations seeking to fortify their cyber defenses.
 Jake Lloyd Then & Now!
Jake Lloyd Then & Now! Mackenzie Rosman Then & Now!
Mackenzie Rosman Then & Now!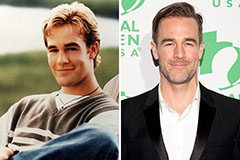 James Van Der Beek Then & Now!
James Van Der Beek Then & Now! Mason Reese Then & Now!
Mason Reese Then & Now! Lacey Chabert Then & Now!
Lacey Chabert Then & Now!